In this activity, you will use tcpdump, a program which prints out the
contents of packets in a vaguely human-readable form.
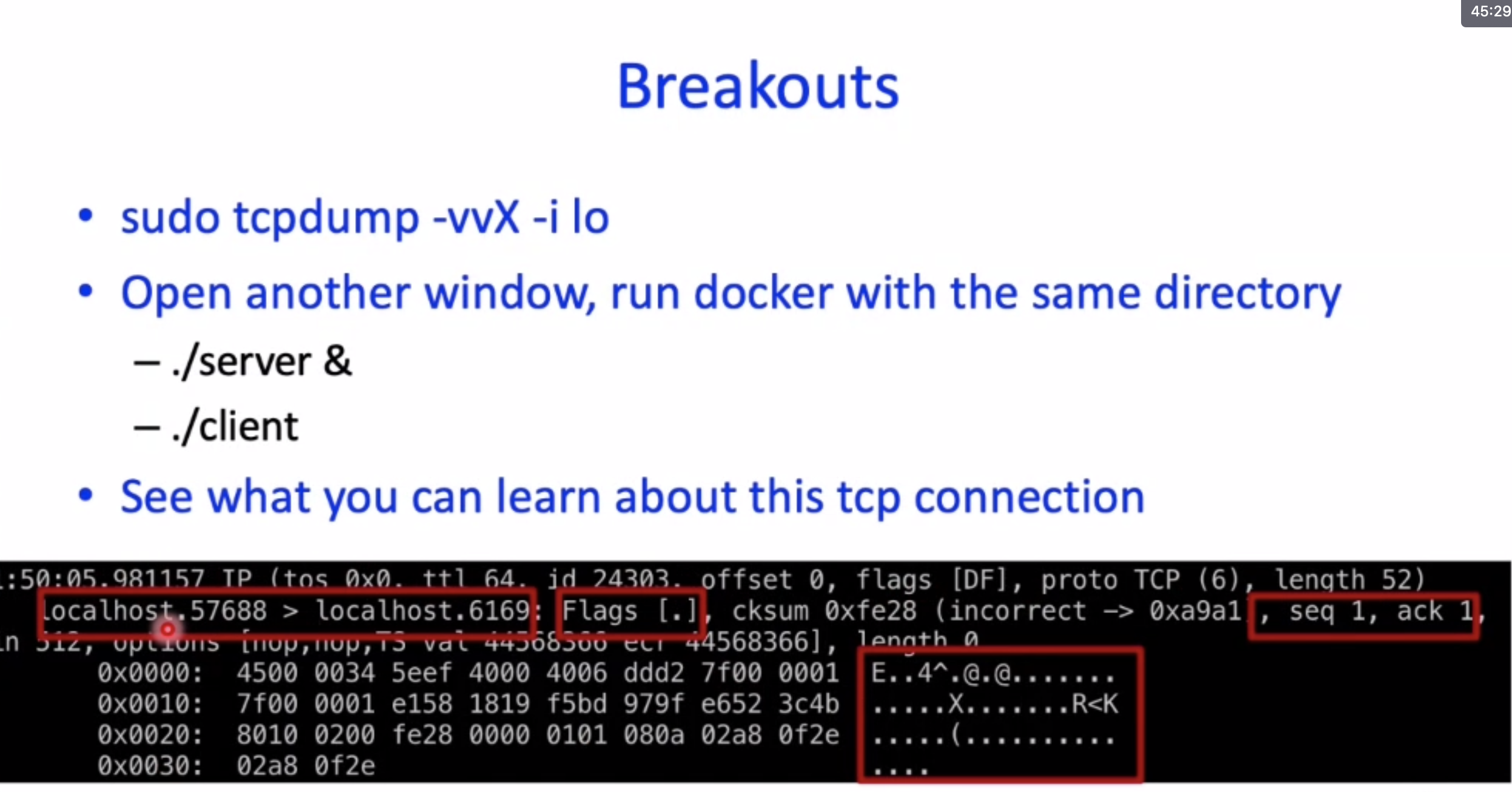
We’d like you to follow these steps.
If you’re using Docker, open two terminal windows, running in the same Docker container (which is indicated by the same prompt, e.g.,
cs61-user@4bccf0c1538a:). This should happen automatically if yourcs61-docker-versionis 5. If you’re using a VM, just open two terminal windows.In window 1, run the
sudo tcpdump -vvX -i locommand. This starts thetcpdumpprogram, and asks it to print a ton of data (vv) for packets that are sent over the operating system’s internal “loopback” network (-i lo).In window 2, run
./server &. Then check what window 1 prints. Then run./client. Then check what window 1 prints.
Tcpdump prints out a lot of information. Don’t worry! You could figure all of it out if you had to; for now, we want you to look for patterns. Some example questions:
How many messages are sent before the payload (the actual message data written by the applications)?
How many messages are sent after the payload ends?
How far into each packet does the payload begin?
How can you distinguish messages from client to server, from messages sent in the other direction? (Hint: The server is using port 6169.)
How do the sequence numbers (
seq) and acknowledgement numbers (ack) change over the course of the connection?How do the flags (
Flags [.]) change over the course of the connection?What else do you see?
